TL;DR:
- Cybersecurity is a vital business risk impacting revenue, reputation, and long-term growth.
- A strategic, layered security approach enhances resilience, compliance, and enables innovation.
- Proactive integration of cybersecurity into business strategy offers competitive advantage and growth opportunities.
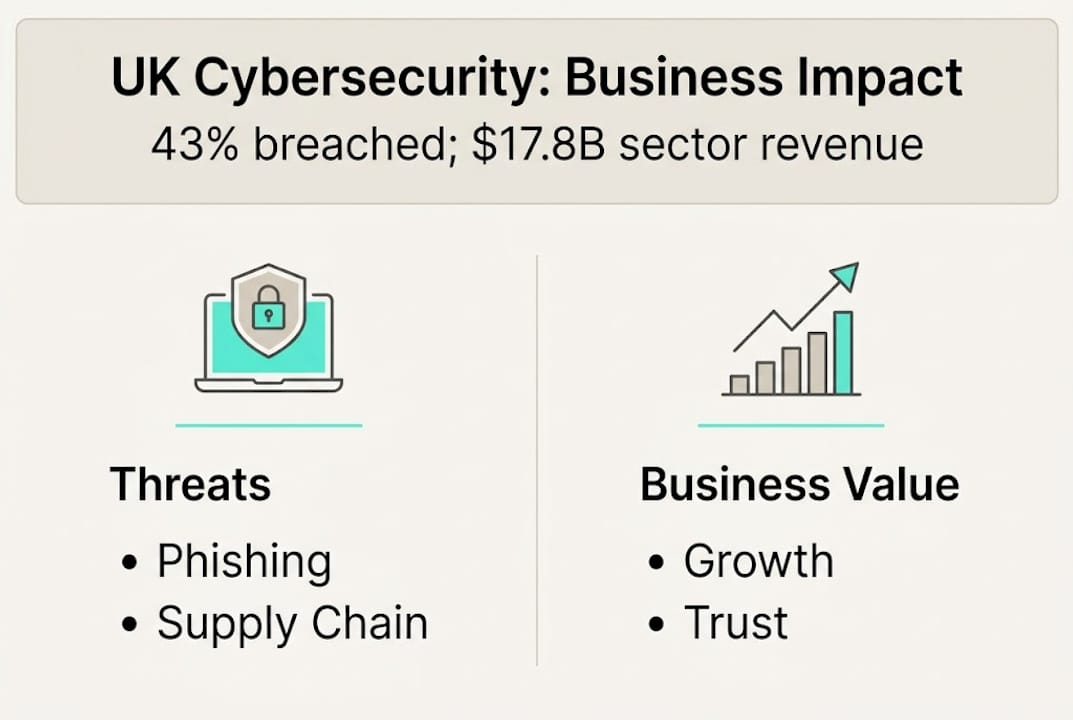
Most business leaders still think of cybersecurity as something the IT department handles quietly in the background. That assumption is costing UK organizations real money. 43% of UK businesses experienced breaches in 2025, with disruptive incidents averaging £1,600 each in direct costs alone. The reputational damage, operational downtime, and lost customer trust rarely show up in that figure. This article cuts through the noise to show why cybersecurity is no longer a technical checkbox but a core driver of business resilience, competitive advantage, and long-term growth for UK organizations.
Table of Contents
- Why cybersecurity matters for UK businesses today
- Core roles of cybersecurity: Beyond protection
- Building a resilient security posture: Essential strategies
- Evolving threats and future trends in cybersecurity
- The uncomfortable truth: Cybersecurity is a growth driver, not just a cost
- Ready to strengthen your business with cyber resilience?
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Business imperative | Cybersecurity is vital for maintaining operations, reputation, and trust in UK organizations. |
| Strategic value | Modern security enables growth, innovation, and compliance—not just protection. |
| Practical frameworks | National standards like Cyber Essentials and supply chain vigilance boost real-world resilience. |
| Future focus | Adapting to new threats and AI-driven risks is the next frontier for business success. |
Why cybersecurity matters for UK businesses today
The numbers tell a clear story. Cyberattacks are not rare events that happen to other companies. They are a routine business risk that boards, finance leaders, and operations teams must factor into every major decision.
| Threat type | Prevalence among UK businesses |
|---|---|
| Phishing attacks | 85% of breached businesses |
| Malware and ransomware | 21% of breached businesses |
| Denial of service attacks | 17% of breached businesses |
| Supply chain compromise | Growing year on year |
The financial exposure goes well beyond the average incident cost. A serious breach can trigger regulatory fines under UK GDPR, legal fees, customer compensation, and months of recovery work. Smaller organizations often underestimate this exposure until they are living through it.
"Cybersecurity is no longer an IT issue. It is a board-level business risk that affects revenue, reputation, and regulatory standing."
Customer trust is equally at stake. When a breach becomes public, the damage to your brand can outlast the technical recovery by years. Clients, partners, and investors all reassess their relationship with an organization that has failed to protect sensitive data.
The case for investment is growing stronger. One in three small businesses faced cyberattacks in the past year, and 94% of business owners now view cybersecurity as critical to their operations. That shift in perception is significant. It reflects a growing awareness that security is not just about keeping attackers out. It is about keeping the business running, maintaining contracts, and protecting the relationships that drive revenue.
The key reasons UK businesses are increasing security investment include:
- Regulatory pressure: UK GDPR, NIS2 alignment, and sector-specific compliance requirements
- Client and partner demands: Enterprise clients increasingly require security certifications before signing contracts
- Operational continuity: Downtime from a breach costs far more than prevention
- Cyber insurance requirements: Insurers now require demonstrable security controls before offering coverage
Understanding how to protect UK business infrastructure starts with accepting that the threat landscape is not going to simplify. It is going to get more complex, and businesses that treat security as a background function will pay the price.
Core roles of cybersecurity: Beyond protection
The traditional view of cybersecurity is purely defensive: build a wall, keep attackers out, and hope nothing gets through. That model is outdated. Forward-thinking UK businesses are repositioning cybersecurity as a strategic enabler that touches every part of the organization.
| Traditional approach | Strategic approach |
|---|---|
| Reactive to incidents | Proactive risk management |
| IT department responsibility | Board-level ownership |
| Compliance-driven | Business-value driven |
| Cost center mindset | Growth enabler mindset |
| Technology focus only | People, process, and technology |
The business-value roles cybersecurity plays are broader than most leaders realize:
- Resilience: A strong security posture means faster recovery from disruptions, keeping operations running when incidents occur.
- Regulatory compliance: Meeting GDPR, Cyber Essentials, and sector frameworks protects the business from fines and opens doors to regulated markets.
- Customer trust: Demonstrable security practices are increasingly a sales differentiator, especially in B2B relationships.
- Innovation enablement: Secure cloud environments and protected data pipelines allow businesses to adopt new technologies without introducing unacceptable risk.
The alignment gap is striking. Only 27% of leaders report strong alignment between cybersecurity and business strategy. That means nearly three in four organizations are running their security function in a silo, disconnected from the decisions that shape revenue, operations, and growth.
Effective IT management strategies bridge this gap by framing cyber risk in business language: potential revenue loss, contract exposure, and reputational impact rather than technical vulnerability scores.
Pro Tip: Invite your cybersecurity lead into major business decisions, whether that is a new supplier relationship, a cloud migration, or a product launch. Security input at the planning stage is exponentially cheaper than remediation after the fact.
The organizations that are winning with cybersecurity are those that have connected it to the technology trends in 2026 shaping their industry. AI adoption, remote work infrastructure, and cloud-first strategies all carry security implications. Treating those implications as a business consideration rather than a technical footnote is what separates resilient organizations from vulnerable ones.
Building a resilient security posture: Essential strategies
Knowing that cybersecurity matters is not enough. The real question is how to build a posture that actually holds up when attackers probe your systems. Here are the strategies that deliver measurable resilience.
Start with recognized frameworks. The NCSC Cyber Essentials and CAF frameworks give UK businesses a structured, government-backed foundation. Cyber Essentials covers five core controls: firewalls, secure configuration, access control, malware protection, and patch management. The Cyber Assessment Framework goes deeper for critical infrastructure and regulated sectors.
Layer your defenses. No single control stops every attack. A layered approach includes:
- Multi-factor authentication on all critical systems and remote access
- Network segmentation to limit the blast radius of any breach
- Encryption for data at rest and in transit
- A tested incident response plan that the whole leadership team understands
- Regular vulnerability scanning and penetration testing
Build a security culture. Technology alone will not protect you. Supply chain compromise remains a persistent weakness, and most breaches still involve a human element: a clicked phishing link, a reused password, or an unvetted supplier. Regular staff training, phishing simulations, and clear reporting processes turn your people from a vulnerability into a line of defense.

Manage your supply chain risk. Proactive supplier assessment is far more effective than reactive damage control. Before onboarding a new vendor, check their security certifications, ask about their incident response processes, and include security obligations in contracts.
Pro Tip: Run a live tabletop simulation with your leadership team at least once a year. Walk through a realistic breach scenario and test your response plan. The gaps you find in a simulation are far cheaper to fix than the ones you discover during an actual incident.
For growing businesses, the right IT support for SMEs can make the difference between a manageable incident and a business-threatening one. And as you scale, integrating security into your digital transformation strategies from day one prevents the costly retrofitting that derails so many modernization programs.
Evolving threats and future trends in cybersecurity
The threat landscape in 2026 looks meaningfully different from even two years ago. Attackers are faster, more automated, and increasingly leveraging AI to scale their operations. Understanding what is coming helps you allocate resources where they will matter most.
The key threats shaping the current environment include:
- AI-powered phishing: Attackers now generate highly personalized, convincing phishing emails at scale using large language models. The days of spotting a breach attempt by its poor grammar are largely over.
- Supply chain exploits: Compromising a trusted supplier to reach multiple downstream targets is now a preferred attack vector for sophisticated threat actors.
- Ransomware as a service: Criminal groups offer ransomware tools on a subscription basis, lowering the technical barrier for attackers and increasing the volume of incidents.
- Identity-based attacks: Credential theft and session hijacking are replacing brute-force methods as attackers target the human layer rather than the perimeter.
"AI disrupts the attacker-defender balance in the short term, but the long-term advantage favors defenders who are armed with data and context."
That is an important signal for business leaders. Investing in threat intelligence, behavioral analytics, and AI-assisted detection now positions your organization on the right side of that long-term shift.
The economic opportunity is also real. The UK cyber sector generated $17.8B in revenue and supported 67,300 jobs in 2024. A growing domestic security ecosystem means better access to specialist talent, innovative tools, and government-backed support programs.
The businesses that will navigate this environment successfully are those tracking cybersecurity trends for 2026 and building adaptive strategies rather than static defenses. Reactive security is always one step behind. Proactive security is what keeps you ahead.
The uncomfortable truth: Cybersecurity is a growth driver, not just a cost
Here is something most cybersecurity conversations avoid saying directly: treating security as an insurance policy is a strategic mistake. Insurance is something you hope never to use. A well-built security posture is something you use every single day, in every customer conversation, every contract negotiation, and every new market you enter.
We see this pattern consistently. Organizations that experience a breach and then invest heavily in security are doing the right thing, but they are doing it at the worst possible time. They are paying a premium in reputation, revenue, and recovery costs before they get to the benefits that proactive investment would have delivered from the start.
Some businesses underinvest because they see cybersecurity as a cost rather than an opportunity. The UK government's own growth action plan identifies this as a structural barrier to national cyber resilience. The fix is not just better compliance incentives. It is a fundamental shift in how leadership frames the value of security investment.
The companies that align cyber with business strategy gain a durable competitive advantage. They win regulated contracts, retain enterprise clients, and scale new technologies faster because their foundations are secure. Understanding technology's role in business growth means recognizing that security is not separate from growth. It is what makes growth sustainable.
Ready to strengthen your business with cyber resilience?
Waiting for an incident to prompt action is one of the most expensive decisions a business leader can make. The good news is that building a strong security posture does not require starting from scratch or navigating complex frameworks alone.
At Mightyskytech, we work with UK businesses to design and implement cybersecurity strategies that align with your operations, your compliance obligations, and your growth plans. From Cyber Essentials certification to full managed security support, we help you build resilience that actually works in practice. Explore how our cybersecurity support for UK businesses can give your organization the protection and confidence it needs to grow without unnecessary risk.
Frequently asked questions
What are the biggest cybersecurity threats to UK businesses in 2026?
The main threats include AI-driven phishing attacks, supply chain vulnerabilities, and ransomware targeting both large and small organizations. As AI shifts the attacker-defender balance, businesses need adaptive defenses rather than static ones.
How can small businesses improve their cybersecurity on a budget?
Small businesses should start with Cyber Essentials, train staff to spot phishing, and keep backups and firewalls updated for basic protection. Given that one in three small businesses faced attacks last year, even basic controls deliver significant risk reduction.
What cybersecurity frameworks should UK firms prioritize?
UK businesses should prioritize the NCSC Cyber Essentials and CAF frameworks for strong, government-recognized protection that also satisfies many client and regulatory requirements.
Why is aligning cybersecurity with business strategy important?
Alignment ensures cyber efforts directly protect revenue, reputation, and operations rather than being treated as a separate IT expense. With only 27% of leaders reporting strong alignment, most organizations have significant room to capture this advantage.