When 93% of UK businesses experience critical cybersecurity incidents annually, the question shifts from whether to invest in protection to how quickly you can implement it. Cybersecurity is no longer a luxury reserved for tech giants or government agencies. For UK corporate decision-makers, understanding why robust cybersecurity matters directly impacts your ability to protect infrastructure, maintain compliance, and ensure operational continuity. This guide breaks down the compelling reasons why cybersecurity is essential for your organization's survival and growth in an increasingly hostile digital landscape.
Table of Contents
- Key takeaways
- The real threat landscape for UK businesses
- Understanding UK cybersecurity regulations and compliance requirements
- Core cybersecurity controls and frameworks: What businesses need to implement
- The business case: Financial benefits and ROI of cybersecurity investment
- Secure your business with Mighty Sky Technologies
- Why use cybersecurity FAQ
Key Takeaways
| Point | Details |
|---|---|
| High incident rate | 93 percent of UK businesses experience critical cybersecurity incidents annually, underscoring the need to act quickly to implement protections. |
| Regulatory fines | The Cyber Security and Resilience Bill mandates fines up to 17 million pounds or 4 percent of global turnover for failing to meet minimum security standards. |
| Core security controls | Implementing core security controls can prevent the majority of attacks and help win government contracts. |
| Supply chain accountability | Regulations extend security responsibility to suppliers and partners, making third party breaches trigger penalties. |
| Strong ROI | Cybersecurity investments yield substantial financial returns and fuel business growth. |
The real threat landscape for UK businesses
The digital threat environment facing UK organizations has intensified dramatically. Beyond the alarming statistic that 93% of UK businesses report critical incidents, half of these companies experience actual breaches that compromise sensitive data, disrupt operations, and damage customer trust. These are not abstract possibilities but documented realities affecting businesses across every sector and size category.
The most prevalent threats targeting UK companies include:
- Phishing attacks that exploit human psychology to gain unauthorized access
- Ransomware campaigns that encrypt critical data and demand payment for restoration
- Insider threats from employees, contractors, or partners with legitimate access
- Supply chain compromises that infiltrate through trusted third-party connections
- Advanced persistent threats that remain undetected for months while extracting valuable information
The financial consequences extend far beyond immediate recovery costs. Companies face regulatory fines, legal liability, customer compensation, business interruption losses, and long-term reputational damage that erodes market position. A single breach can cost millions in direct expenses while destroying years of brand equity built through consistent service delivery.
"The average cost of a data breach in the UK now exceeds £3.5 million when you account for notification requirements, forensic investigation, system restoration, legal fees, regulatory penalties, and customer churn."
Legacy systems compound these vulnerabilities significantly. Many UK businesses operate critical infrastructure on outdated platforms that lack modern security features, receive no vendor support, and contain known exploitable weaknesses. Social engineering remains devastatingly effective because attackers recognize that technology alone cannot protect against manipulation of human trust and authority structures.

The sophistication gap between attackers and defenders continues widening. Criminal organizations now operate with corporate structures, specialized roles, and substantial budgets dedicated to developing new exploitation techniques. Meanwhile, many businesses struggle to maintain basic security hygiene due to resource constraints, competing priorities, and insufficient understanding of risk exposure.
Understanding UK cybersecurity regulations and compliance requirements
The UK government has responded to escalating cyber threats with comprehensive legislation that fundamentally changes compliance obligations for businesses. The Cyber Security and Resilience Bill mandates fines up to £17 million or 4% of global turnover for organizations that fail to meet minimum security standards, particularly those operating critical national infrastructure or handling sensitive data.
This regulatory framework extends responsibility beyond your immediate organization. You must now ensure that suppliers, vendors, and partners throughout your entire supply chain maintain adequate security controls. Third-party breaches that compromise your systems or data trigger the same penalties as direct failures, creating cascading accountability that requires rigorous vendor assessment and ongoing monitoring.
Key enforcement mechanisms include:
- Mandatory incident reporting within 72 hours of detection
- Regular security audits and compliance assessments
- Board-level accountability for cybersecurity governance
- Public disclosure requirements for significant breaches
- Personal liability for directors in cases of gross negligence
The regulatory landscape encompasses multiple overlapping frameworks that collectively define your obligations:
| Regulation | Scope | Maximum Penalty | Key Requirements |
|---|---|---|---|
| Cyber Security and Resilience Bill | Critical infrastructure, digital services | £17m or 4% global turnover | Supply chain security, incident reporting, risk management |
| UK GDPR | Personal data processing | £17.5m or 4% global turnover | Data protection, breach notification, privacy by design |
| Network and Information Systems Regulations | Essential services, digital providers | Unlimited fines | Security measures, incident handling, supply chain oversight |
| Payment Card Industry Data Security Standard | Card payment processing | Loss of processing privileges | Encryption, access controls, network segmentation |
Compliance is not a one-time achievement but an ongoing process requiring continuous monitoring, regular updates, and adaptive responses to emerging threats. The regulatory burden may seem overwhelming, yet it reflects the severity of risks facing modern businesses and the societal impact of inadequate protection.
Government contracts now routinely require Cyber Essentials certification as a minimum qualification, effectively excluding non-compliant organizations from significant revenue opportunities. This creates a competitive disadvantage that extends beyond regulatory penalties into lost business development and market access.
Core cybersecurity controls and frameworks: What businesses need to implement
The UK's National Cyber Security Centre provides clear guidance on fundamental protections through its Cyber Essentials program. NCSC's Cyber Essentials includes five core controls: firewalls, secure configuration, update management, access control, and malware protection. These controls address the most common attack vectors and prevent the vast majority of opportunistic threats.
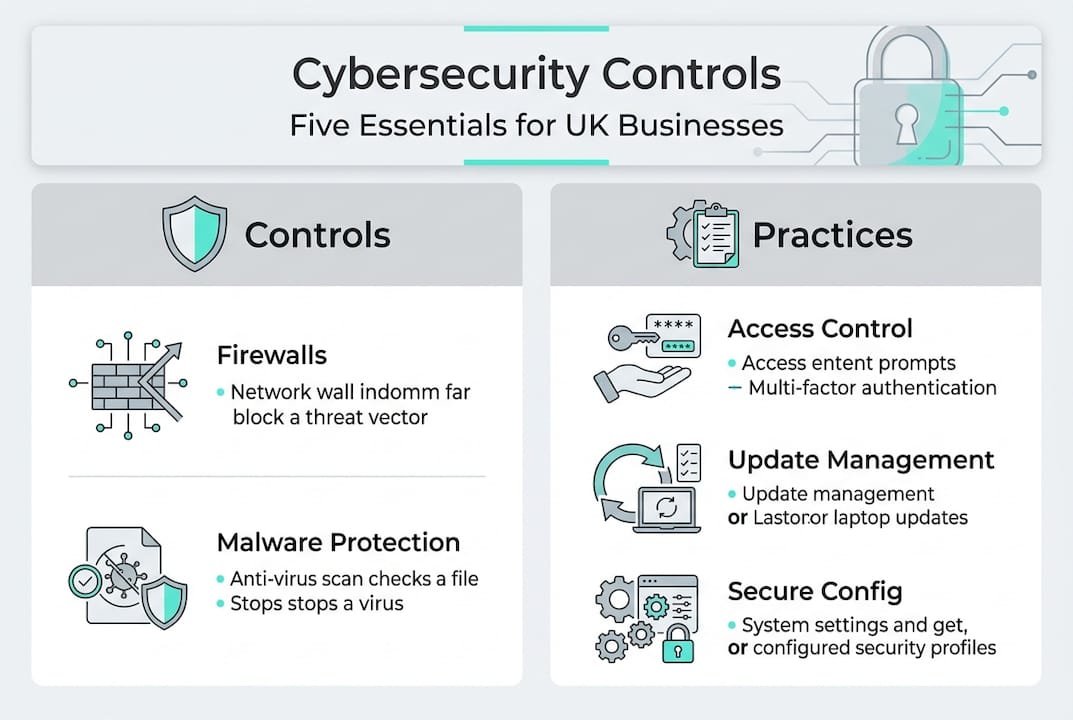
Firewalls establish boundaries between trusted internal networks and untrusted external connections, filtering traffic based on predefined security rules. Proper configuration blocks unauthorized access attempts while allowing legitimate business communications to flow freely.
Secure configuration eliminates unnecessary services, removes default credentials, and hardens systems against exploitation. Many breaches succeed because attackers exploit well-known vulnerabilities in default settings that organizations never changed after initial deployment.
Update management ensures that software patches addressing known security flaws get applied promptly across all systems. Attackers actively scan for unpatched vulnerabilities, making timely updates one of the most effective defensive measures available.
Access control implements the principle of least privilege, granting users only the permissions necessary for their specific roles. This limits damage from compromised accounts and reduces insider threat exposure significantly.
Malware protection deploys multiple layers of defense including endpoint detection, email filtering, web gateway security, and behavior analysis to identify and block malicious software before it executes.
Pro Tip: Prioritize Cyber Essentials certification first because it satisfies government contract requirements while establishing a solid security foundation. You can then layer additional controls based on your specific risk profile and industry requirements.
| Framework | Primary Focus | Best Suited For | Complexity |
|---|---|---|---|
| Cyber Essentials | Basic hygiene controls | Small to medium businesses, government contractors | Low |
| ISO 27001 | Comprehensive information security management | Large enterprises, regulated industries | High |
| NIST Cybersecurity Framework | Risk-based security program | Organizations seeking flexible implementation | Medium |
| CIS Controls | Prioritized defensive actions | Technical teams building security programs | Medium |
Modern security thinking has evolved beyond perimeter defense toward zero trust architecture. This approach assumes breach is inevitable and implements continuous verification, micro-segmentation, and least-privilege access regardless of network location. Rather than trusting everything inside your firewall, zero trust requires authentication and authorization for every access request.
The assume-breach posture shifts focus from prevention alone to detection and response capabilities. You need visibility into network traffic, user behavior, and system activities to identify anomalies that indicate compromise. Rapid incident response limits damage by containing threats before they spread throughout your infrastructure.
The business case: Financial benefits and ROI of cybersecurity investment
Cybersecurity delivers measurable financial returns that extend far beyond avoided breach costs. Cybersecurity investments have fueled a £27 billion revenue boost for UK firms, with 53% reporting turnover increases directly attributed to improved security posture. This demonstrates that protection is not merely a defensive expense but a strategic enabler of business growth.
The return on investment calculation becomes compelling when you compare security spending against breach costs. Organizations implementing comprehensive controls achieve potential 261% ROI through risk reduction, operational efficiency gains, and competitive advantages in customer acquisition.
Financial and operational benefits include:
- Enhanced customer confidence leading to increased sales and retention
- Reduced insurance premiums through demonstrated risk management
- Faster incident response minimizing business disruption duration
- Improved operational efficiency from streamlined security processes
- Access to new markets requiring security certifications
- Competitive differentiation in industries where trust matters
- Lower cost of capital from reduced risk profile
- Attraction and retention of top talent seeking stable employers
Strategic Impact: Companies with mature cybersecurity programs report 15% higher profit margins compared to industry peers, reflecting both cost avoidance and revenue enhancement from security-enabled business opportunities.
The cost of inadequate protection far exceeds investment in proper controls. Beyond direct breach expenses, organizations suffer productivity losses during recovery, opportunity costs from diverted resources, and strategic setbacks from delayed initiatives. Customers increasingly evaluate security posture when selecting vendors, making protection a competitive requirement rather than a technical consideration.
Viewing cybersecurity as a strategic enabler rather than a cost center transforms how you approach investment decisions. Security becomes integrated into business planning, product development, and customer engagement strategies. This perspective shift unlocks innovation opportunities while maintaining the protection necessary for sustainable growth.
Board-level engagement with cybersecurity governance signals organizational commitment that resonates with customers, partners, and investors. Companies demonstrating mature security practices command valuation premiums in mergers and acquisitions, reflecting reduced risk and enhanced operational capabilities.
Secure your business with Mighty Sky Technologies
Navigating the complex cybersecurity landscape requires expertise, experience, and dedicated resources that many organizations struggle to maintain internally. Mighty Sky Technologies Limited specializes in comprehensive IT security solutions tailored specifically for UK businesses facing the challenges outlined throughout this guide.
Our team brings deep knowledge of UK regulatory requirements, threat landscapes, and implementation best practices to help you build robust defenses that protect infrastructure while enabling business growth. We work alongside your leadership to develop security strategies aligned with organizational objectives, ensuring protection supports rather than hinders operational goals. From initial risk assessment through ongoing managed security services, we provide the expertise needed to maintain compliance and resilience in an evolving threat environment.
Why use cybersecurity FAQ
What makes cybersecurity essential for small UK businesses if large enterprises are the primary targets?
Small businesses actually face higher breach rates because attackers perceive them as easier targets with weaker defenses. You also serve as entry points into larger corporate supply chains, making you valuable for indirect attacks. Implementing basic controls costs far less than recovering from a breach that could force business closure.
How do I know if my current cybersecurity measures meet UK legal requirements?
Start with Cyber Essentials certification, which establishes baseline compliance for most UK regulations. Conduct a gap analysis against specific requirements applicable to your industry, such as GDPR for personal data or NIS Regulations for essential services. Professional assessment identifies vulnerabilities before regulators or attackers do.
Can cybersecurity investments really generate positive ROI beyond avoiding breach costs?
Yes, through multiple channels including competitive advantages in customer acquisition, access to government contracts requiring certifications, reduced insurance premiums, and operational efficiencies from streamlined processes. Security-conscious organizations report measurable revenue growth as customers increasingly prioritize vendor trustworthiness.
What should be my first priority when building a cybersecurity program from scratch?
Implement the five Cyber Essentials controls first because they address the most common attack vectors cost-effectively while satisfying government contract requirements. Focus on asset inventory, access management, and update processes before pursuing advanced capabilities. Building a solid foundation prevents the majority of threats you will encounter.
How do I secure my supply chain when I cannot control third-party security practices?
Establish contractual requirements for minimum security standards, conduct regular vendor assessments, implement network segmentation to limit third-party access, and maintain incident response procedures for supply chain compromises. The new UK regulations make you responsible for supplier security, requiring due diligence and ongoing monitoring throughout vendor relationships.
Why do legacy systems create such significant security risks even with modern perimeter defenses?
Legacy platforms often lack fundamental security features, receive no vendor patches for newly discovered vulnerabilities, and cannot integrate with modern security tools for monitoring and protection. Attackers specifically target these systems because exploitation techniques are well-documented and defenses are limited. Migration planning becomes essential for long-term security posture.
